Monarx 2025 Security Landscape Report
Thank you for your interest in the detailed research conducted by the Monarx Security Team. Below, you’ll find a more technical version of our white paper, offering expanded explanations and deeper insights into each section.
Before we dive in, here is a short introduction to what Monarx is:
Monarx delivers next‑generation, AI‑powered server and application security purpose‑built for the modern Linux hosting stack. Using advanced behavioral detection, Monarx identifies threats that traditional scanners miss and automatically removes them—without disrupting customer sites. With a lightweight footprint and real‑time protection, Monarx helps hosting providers stop zero‑day attacks, reduce infections, and significantly cut down on support workloads. Monarx is trusted by leading hosting companies worldwide, including Hosting.com, Namecheap, Hostinger, Newfold Digital, and many others. Want to see how it works? Sign up here.
As a leader in enterprise-grade security for the web hosting industry, Monarx operates on a global scale that provides unparalleled visibility into the evolution of digital threats. During 2025 alone, our centralized cloud platform processed nearly 9 trillion file signals and conducted over 500 billion real-time analyses. This massive data ingestion allowed our signature-less cloud engines to classify more than 8 billion unique files and successfully identify novel malware in over 100 million previously undocumented cases.
Beyond simple detection, Monarx took proactive measures by remediating over 2 billion existing infections and preemptively terminating more than 3 billion malicious runtime operations. By stopping these attacks before they could result in system compromise or server abuse, we have gathered unique insights into the global malware landscape —insights we are proud to share in this report.
Malicious vs Injected Files
The 2025 data demonstrates that signature-based "delete-only" security is no longer sufficient. As attackers increasingly favor compromising legitimate files during peak traffic periods, the ability to perform automated, surgical remediation—the hallmark of the Monarx platform—has become the industry standard for maintaining uptime during the most volatile months of the year.
To understand the 2025 data, we must first distinguish between two primary categories of threats that we use in Monarx: Malicious Files and Injected Files.
- Malicious Files: These are files created entirely by an attacker (e.g., uploaders and backdoors). They serve no legitimate purpose and are designed to be deleted entirely.
- Injected Files: These are legitimate WordPress core files or plugin/theme components (e.g.,
index.phporfunctions.php) that have been "backdoor-injected" with malicious snippets. These require surgical remediation—removing the bad code while preserving the file's original functionality.
With these categories defined, we can now examine how they behaved across the 2025 threat landscape.
Malware activity observed in 2025
Throughout 2025, we observed a distinct correlation between the type of threat detected and the time of year. While "Injected" file uploads remain relatively steady, "Malicious" file detections show a dramatic upward trend around the Q4 holidays.
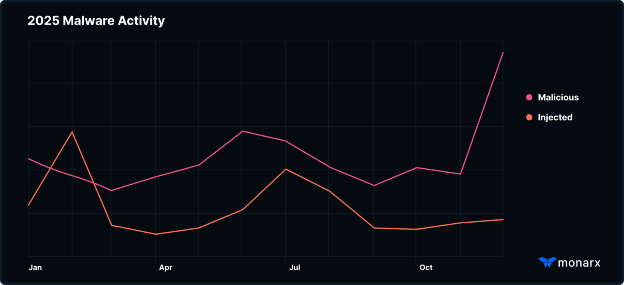
This "Holiday Spike" is driven by a convergence of high-volume consumer traffic and reduced institutional oversight. Bad actors capitalize on diminished administrative response times,while IT teams are at minimum capacity; attackers automate the injection of legitimate files to hide their tracks.
Threat Landscape Data
Behind every trillion signals processed by our cloud lies a sophisticated narrative of how modern attackers operate. In this section, we transition from global statistics to granular forensics, providing a deep dive into the specific artifacts and behaviors that defined 2025.
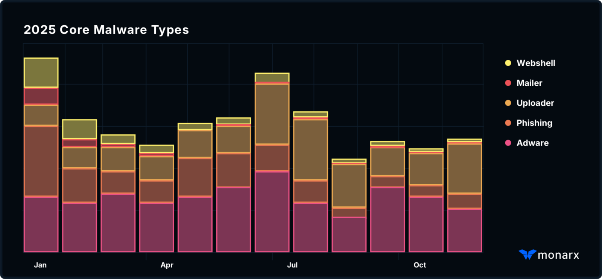
Our telemetry identified Adware as the most prevalent malware category, representing a consistent baseline of high-volume, automated threats targeting the WordPress ecosystem. However, the most significant shift in the landscape occurred during the summer: Uploader scripts saw a dramatic surge in June 2025, nearly doubling their presence within a single thirty-day window. Rather than a temporary spike, this increased volume was maintained throughout the remainder of the year. This sustained footprint suggests a strategic pivot by threat actors, who utilized these persistent uploaders as the foundational infrastructure for more complex, multi-stage attacks and the subsequent deployment of various secondary payloads.
Trending Malware Campaigns
To better understand these shifts, we analyzed the campaigns and code sequences most responsible for shaping the 2025 threat landscape. By analyzing the most frequent Malicious Sequences, Standalone Malicious, Injected files, and Surgical Injections, we offer the WordPress community a transparent look at the "Top Malware Trends" emerging from our global telemetry. These analyses are designed to help organizations understand the current trajectory of cyber threats and, more importantly, how to evolve their defensive posture to stay ahead of them.
We will break this data down into four critical pillars:
- Top Malicious Sequences: The behavioral patterns and "chains of command" used to orchestrate an attack.
- Top Malicious Files: Standalone assets built entirely for harm and persistence.
- Top Injected Files: Legitimate WordPress components most frequently weaponized by attackers.
- Top Injections: The specific snippets of code used to hijack functionality without alerting the site owner.
In each subsequent section, we will examine thoroughly each pillar and provide real-life examples that we observed.
Top Malicious Sequences
Monarx uses a proprietary approach to categorizing malware based on its behavior. We call these sequences. The tops sequences found in 2025 are displayed below. Notably, the top 8 (colored in blue) sequences all belong to Japanese SEO family.

What is the Japanese SEO Poisoning kit?
The Japanese-Targeted SEO malware campaign hijacks a site's search engine reputation to serve malicious content to bots while redirecting real Japanese users to a "jump" page — likely a phishing site or a fraudulent "Japanese Pharmacy" store. They begin disabling any error, setting PHP's time limit to 120 seconds and keeping the hack running even after the visitor closes the tab/window. Then the script calls home, the top 5 C2 (command and control) Hubs observed were:
hxxps://j251106_23[.]zpollich[.]com
hxxps://j251116_23[.]atelart[.]com.
hxxps://j251212_13[.]campraider[.]com.
hxxp://107.150.48[.]76/j251121_23
hxxps://j251220_23[.]edictions[.]com
After this the script checks if the visitor is a Search Engine or a human; search engines are served targeted keyword-stuff text to rank the site for specific terms, and for humans whose language on their browser is set to Japanese, the user is silently redirected to a destination controlled by the C2 server. It also intercepts requests for robots.txt and sitemap.xml and injects fake content into both files to make sure those fake pages are indexed by Search Engines.
Top Malicious Files by SHA256
Monarx also categorizes malware files by their SHA256 hash. The top SHA256 hashes of malicious files are below. The highest in 2025 was the jgalls SEO malware campaign.
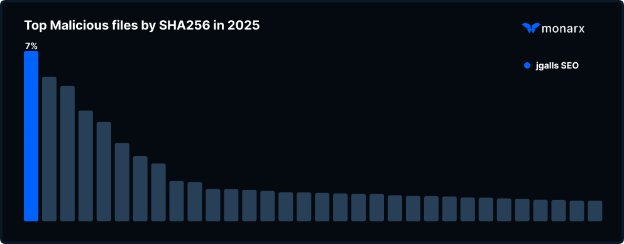
What is jgalls SEO?
Unlike the Japanese SEO kit, this campaign exclusively communicates to a C2 server jgalls[.]com. This infection code uses goto jumps and hexadecimal/octal string encoding (e.g., \110\124\124\120\123) to make it difficult for human administrators and simple scanners to read. It is designed to hijack a site's search engine presence, inject malicious sitemaps, and redirect legitimate visitors to a third-party server (likely for phishing or selling counterfeit goods) while hiding from search engine bots.
This infection locates your robots.txt file, and just like the Japanese infection, it injects fake sitemaps into the file to index thousands of spammy pages that do not actually exist in your file system. The most dangerous feature of this infection is that it checks the user's IP to redirect the request accordingly. If the visitor is a search engine, then it serves a keyword stuffed page retrieved from the C2 server, and if the visitor is a human, it serves a JavaScript redirect to send the visitor to the bad actor's spam site.
Top Injected files by SHA256
Monarx also tracks compromised file SHA256 hashes, the top injected file SHA256 hashes are displayed below. The top two were much more prevalent than the rest were related to the Lock360 Family. This dramatic difference in footprint is caused by the persistence-focused nature of the backdoor, which is engineered to remain in the file system indefinitely.
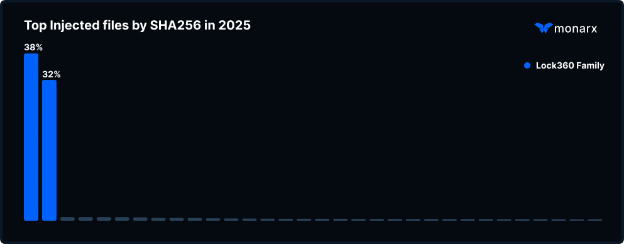
What is Lock360?
The Lock360 malware family is a persistent and aggressive SEO spam and backdoor operation that uses "process-resident" techniques—meaning the malware runs in the server's memory to automatically reinfect files the moment you try to clean them. It follows the same principles as the Japanese and the jgalls campaigns, as it injects sitemaps and robots.txt and uses cloaking to redirect visitors depending on whether they are Search Engines or regular visitors.
The difference is that this infection monitors your index.php and .htaccess files, and if they are modified/restored, this campaign instantly rewrites the infection back into the file since the script is running in the background. Common files used are often named lock360.php, about.php, or radio.php.
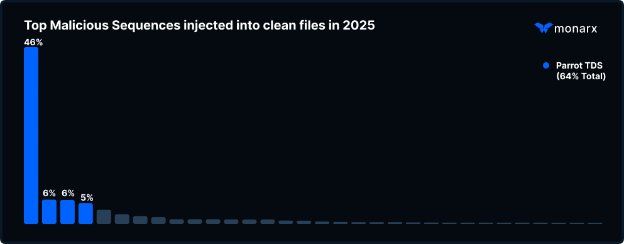
Top Malicious Sequences injected into clean files
Monarx tracks the sequences of malicious code injected into otherwise legitimate files. The top injected sequences for 2025 are shown below. As observed, the top injected sequence in 2025 was Parrot TDS. This injection is uniquely pervasive because it targets all JavaScript files site-wide, making it the most significant threat in terms of total injected assets.
What is Parrot TDS?
Parrot TDS is a sophisticated malware campaign that has been active since at least October 2021. It isn't a single "virus" but rather a global "gatekeeper" system that takes over WordPress sites to filter and route users towards malicious payloads. It essentially inspects every visitor of a compromised site and decides who gets a fake update, who gets a scam, and who is ignored.
The campaign follows a "two-stage" injection process:
- The landing script (often referred to as
ndsjorndsw). Bad actors inject a small piece of JavaScript into all the existing files of the compromised website. This code builds a profile of youby tracking your IP address, browser settings, language, and your history with previous attacks.
- The payload. If you are considered a valuable target, the script calls the payload server, and it renders a second script that redirects your browser to a third-party malicious page.
A notable evolution of this infection is that the most recent versions of this infection campaign are now able to detect AI crawlers (like those used by ChatGPT or Google Gemini) to feed them "clean" content while still serving malware to human users.
Ready for next‑gen AI Server Security?
Start your Monarx journey in minutes
